OOP MAlware Analysis
What IS Different Here
If You Are a new Analyst or you didn’t face the kind of situation where you are required to analyze malware that is written in OOP You will find yourself lost when you are trying to recognize OOP Concepts in Assembly code.
In this blog, I will explain how you can identify these patterns using a malware sample that uses OOP is written in C++ “which we have the source code for”, Some concepts maybe not be presented in the sample so I will demonstrate them from different sources.
note:
I used the Symbols to make it easy as possible to explain but in real life, there will be no symbols
At start, you can beautify the names a little bit in IDA With the following option.
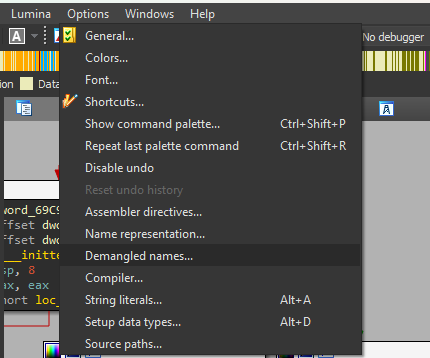
and choose the name radio button.
Object Creation
The first thing to start with is the creation of a new object, The object can be created in Stack or Heap.
ObjA object = new objA;
here is assembly code from inside a function that takes one parameter which is ‘size’ the size of the object, and also inside the function it specifies where to create it “in ecx”.
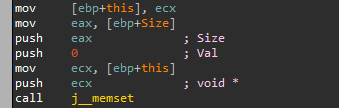
Now you can access members of the object using an index from this pointer.
Constructor
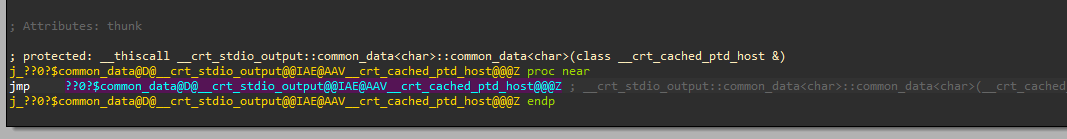
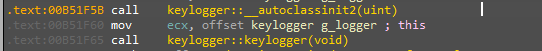
After creating an object the first thig that happens is calling the constructor which simply is a function that has the same name as the class.
In the following picture our object is created with the first function and the ‘g_looger’ is the pointer to it.
Vtable
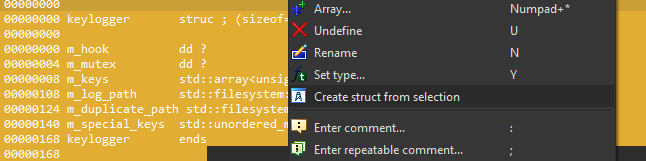
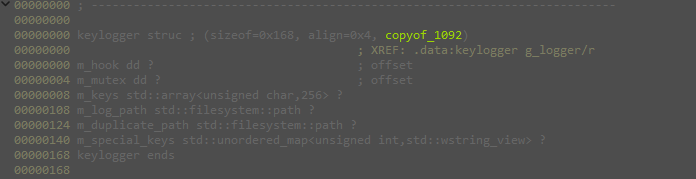
Once you create an object you actually allocate a memory that has a specific structure for that object which contains its members and pointers to its virtual functions. In the Structures tab in ida, you can view the structure for the object ‘Keylogger’
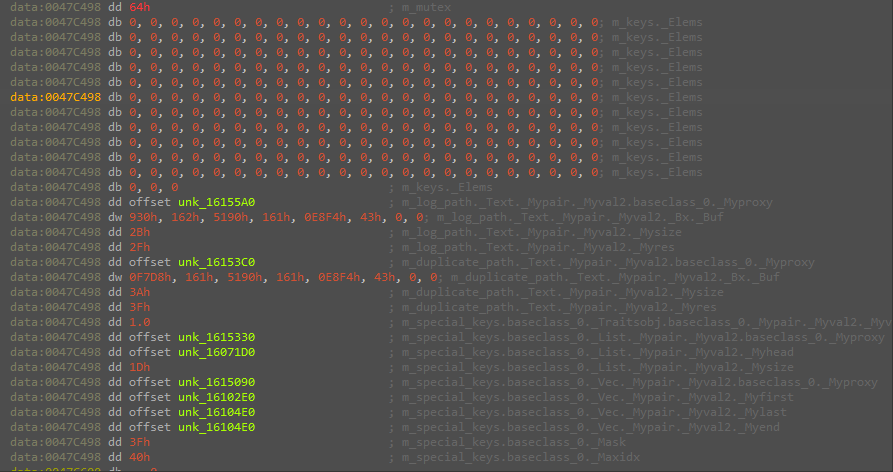
And once the object is created you can see it in the created memory
the calls to the virtual functions will be using an index into the Vtable
note:
If the Vtable is very large to trace manually you can quickly create a structure for it using IDA by highlighting the vtable , right click and choosing 'create structure from selecting'